Cybersecurity Certification Training Program
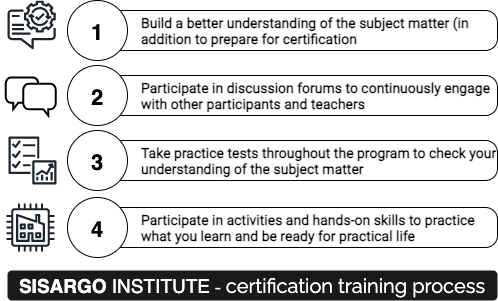
This program is about building a deeper understanding of information security, not just about passing certification exams. That is why it spans over six months to enable participants to take time to build deeper concepts and gain knowledge required to become an excellent professional. During this longer period of time, you will be interacting with instructors and your classmates on a regular basis, doing activities to practice your knowledge, and participate in discussions. This is not bootcamp-style training but a well-planned program to enable you to meet challenges of real life while getting ready to pass the certification exam.
Start Dates
The program starts the first week of every month. There is an upper limit of 25 students for each session (with a minimum of 10 students). Enrolling early helps you reserve your place in the program starting next month.
Program Length
This program is spread over 6 months (24 weeks)
Practice Tests
Throughout the course, participants will do practice tests and understand how to identify correct answers from “distractors” which are the choices that seem to be accurate but are not.
Discussion Forums (Online)
Each participant will get membership of online discussion forums. The purpose of discussion forums is to continuously engage all participants and build a community around learning. They can participate in conversation with trainers as well as other students. They can also post questions for quick answers from the community.
Activities – Learning by doing
Learning by doing is a key focus of every SISARGO Institute training and this is no exception. Participants will be involved in activities, some of those will involve research, others hands-on use of technology, using commands, open source tools and so on.
Outline of the program
The training program is divided into weekly learning objectives, activities and goals. The program will cover domains related to the certification. Please check the following for list of domains covered in each certification.
CISSP
- Introduction to Security and Risk Management
- Asset Security
- Security Architecture and Engineering
- Communication and Network Security
- Identity and Access Management (IAM)
- Security Assessment and Testing
- Security Operations
- Software Development Security
CISM
- Information Security Governance
- Information Risk Management
- Information Security Program Development and Management
- Information Security Incident Management
CISA
- Information System Auditing Process
- Governance and Management of IT
- Information Systems, Acquisition, Development and Implementation
- Information Systems Operations and Business Resilience
- Protection of Information Assets
